Compromised invoices and fraudulent bank transfers
Today I happened to see for the second time the same "Modus Operandi", which worked throught the communication of an invoice with fake bank coordinates between supplier and customer.
Following a payment process violation warning by a company I know, I learned of a second (as far as I know - I have no idea what it's like on a national scale) IT incident with the same procedure.
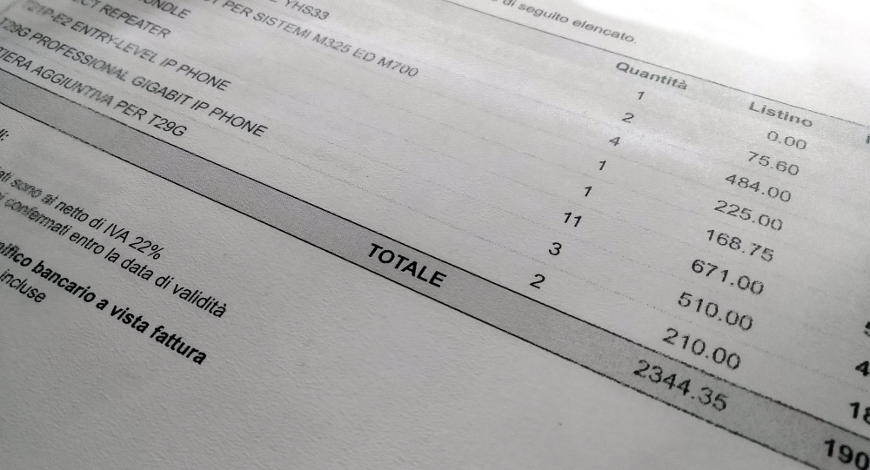
Here is what happens: a service provider sends its invoices via e-mail. The customer validates and verifies it, but shortly after receives another message suggesting to check, as the previous e-mail supposedly had incorrect bank coordinates. A picture with the original invoice with different coordinates is attached to the e-mail. The image file is just the original invoice (usually in PDF format) which has been edited by pasting fake coordinates over the original ones.
In the first case I analysed, everything depended on a weakness in the e-mail provider credentials, which allowed the delinquent to forward all e-mails received by the concerned company. The following communications were sent through a different provider by an e-mail address which had nothing to do with the company one (in the first case, @gmail.com).
In both situations, the procedure described is identical. By analysing the message headers, we ascertained that the e-mails were not being sent from the sender's mail system, but rather from an IP which - according to the Internet registry - is located in Nigeria. We could also ascertain - although this could only be a mere supposition - that both transfers were made through SWIFT rather than SEPA. After a longer and more ample reflectioon, I can also affirm that the two companies both engage in a similar type of activity (despite not being linked to each other).
Even though this is not a direct violation of the company information system (in the first case, it's a violation of the e-mail provider in the cloud, while in the second case we are still analysing the event), the fact that two similar incidents occurred within our small circle of customers, suggests that this could become a wider phenomenon.
01/09/2018 00:00:00