Increased rate of banned IPs for SSH bruteforce
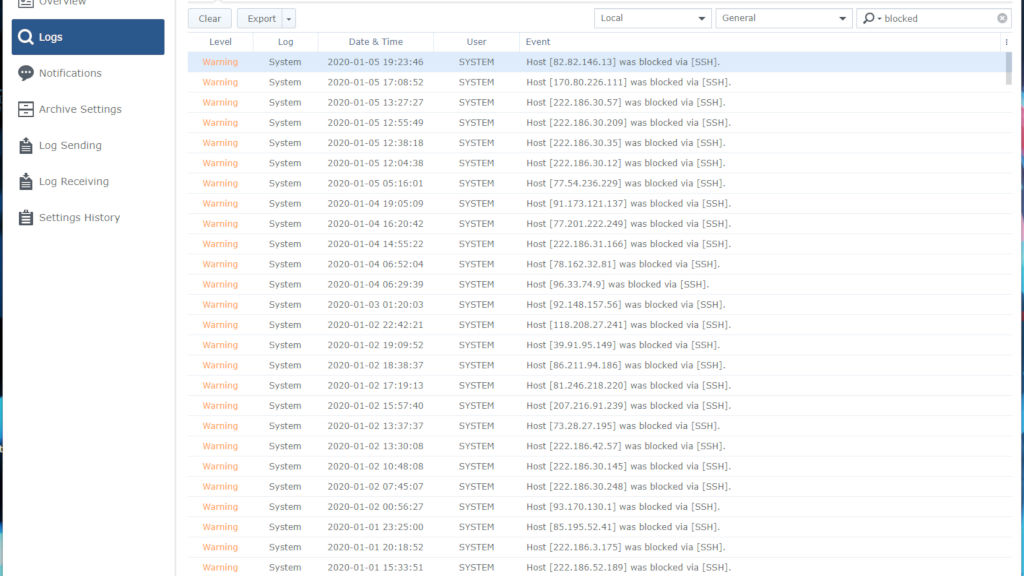
Since the beginning of the year I found an intensive raise of SSH attempts on a home device.
Things always happen for a reason.
One of the very few SSH open devices I own is my home NAS. It's a Synology 415+ DiskStation. As a paranoid policy it has been set up to ban an IP address if a certain amount of login attempts is failed. Since 26th September 2018 it banned 2485 IPs as of now.
Usually it runs at a pace of 1-2 IP addresses banned per day. Since 1st January 2020 the ration has spiked, and it's running on a rate of 8-12 IP addresses per day, which makes me think there is something weird going on.
I have not analysed the morphology of the IP addresses, but that's something I might be doing during next weeks, just for fun.
If you have a Synology device exposed over the Internet and need to have either SSH, FTP or DSM accessible, you may want to be sure to enable the Account Security settings from your Control Panel:
- Control Panel
- Security
- Account
- Enable Auto-Block
- Account
- Security
Also keeping up to date your DSM is something you want to have. One of the key benefits of a Synology device is their security patching policy. Should any serious vulnerability be discovered and documented via a CVE bulletin, within 48 hours you may expect a patch to be released.
More to come but the main reason for this post is: the amount of Cyber Attacks is spiking in the first days of this year.
Keep yourself safe.
05/01/2020 00:00:00