So you caught Cryptowall. Here is where your Infosec failed
The new encrypting virus campaign not only requires a ransom to recover your data, but also shows how things must go bad to make it successful.
Cryptowall is one nasty little virus, born from its older predecessor Cryptolocker. It essentially encrypts all your computer's relevant data, perhaps on network shares too, and therefore leaves a neat (unencrypted) set of files where it asks for a ransom to be paid in order to have your data back. And just like the best Customer Service, it leaves a clean and neat instructions about it, in three different formats: an HTML file, an RTF file and a plain TXT file. Polite isn't it?
So, you want your data back? You got to pay 1 BTC (BitCoin).
And how could that happen? You should not think it came out from nothing, appearing in your computer or network just because of a Solar Flare. It crossed several points of control, and then damaged your data, making it unreadable and technically extremely hard do recover. But You should have a backup copy of your data, perhaps on your NAS... oh... right... in a network share.
Seriously, where did your Information Security fail in your chain?
- Cryptowall spreads itself using an E-Mail campaign using an existing Botnet, attaching executable programs to the message and "crafting" it (i.e. making it look like) a common attachment, like a PDF file mainly. Perhaps the message is well printed too, so you just received a file you should NOT hae in an E-Mail (i.e. an application). Perhaps your provider does not filter properly the attachments or, if you have an E-Mail system on premises, you are not filtering messages properly. Your attachment control policy (or your service provider's one) has failed.
- After a short while the amount of messages sent by the Botnet shall trigger a "SPAM" alert or a "Virus Outbreak Alert", so if you received above e-mail, it means your provider (our yourself) is not equipped with an efficient E-Mail flow control system.The anti-SPAM system, either your or your provider's, has failed.
- Let's say that you allow applications in your e-mails and the Virus Outbreak systems have not triggered ("yes") an alert, there are chances an antivirus on either the mail transport agent or the mail server itself should catch the file and mark it as a Virus. If not, your E-Mail Antivirus control policy failed.
- Your E-Mail client automatically opened the attachment, because the message was "crafted" well enough to make it happen: probably this shouldn't have happened if your e-mail client was properly patched with latest security advisory, which means that your Software Update Policy failed.
- You opened the file yourself, because you are sure that a stranger have sent you a legitimate Invoice or document that you needed to open. I am sorry, but at this point the human error (which - be aware - is plausible) caused a threat event. Which does not mean that you are the cause of the threat because...
- Your local PC antivirus did not intercept the program being executed performing malicious actions. This happens, often, with free Antivirus softwares or wherever an AV software is not present at all. Indeed, this becomes a local Antivirus Policy fail.
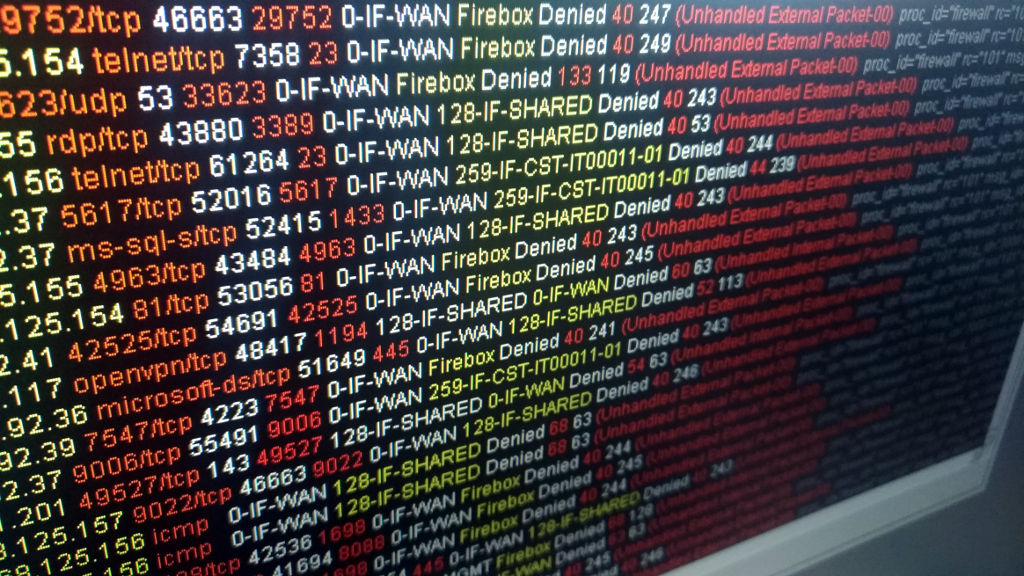
- Cryptowall is running on your computer, and the first thing it does is installing installing a TOR proxy client, which allows it to connect to the TOR network. Since the connection is successfully established, perhaps your network firewall failed to block Peer-to-Peer network connections due to wrong configuration or lack of functionality, indeed this is a new Outgoing Firewall fail.
- The virus created a private key with the remote Command and Control server and started encrypting your data, which also includes the one you store on Dropbox, OneDrive, Google Drive, or any other cloud storage. And once it's complete, you're locked out of your data. But you had that backup on your NAS device which now is... encrypted as well. Here comes a Backup Policy failure.
So, seriously, to get caught in the Cryptowall trap needs a LOT of things to go wrong. And since it's a Computer virus, there are no antibodies developed after the first contagion. Unless you fix the above, you always run the risk of being hit and get to pay a ransom. Again.
How really does such security effort cost? Less than you can imagine, and solutions are wide spread and available, making the investment in security affordable.
A reliable and efficient E-Mail control system that locks out malicious attachments and SPAM messages out of the boundaries of your Network (or ISP if you have your e-mail in Cloud)
An efficient and running Antivirus system running on both Network boundary and client systems that should detect malicious code passing through the network perimeter and trying to get on your endpoint system
A reliable Software Update procedure, that should keep up to date your software, not just for its stability but also to reduce the risk of exploits.
A good support from your IT outsourcing company, so that your employees are aware of possible phishing threats, SPAM messages, and decoys available on the Network: remember that the most efficient way to exploit a company is through "Social Engineering" (i.e. exploiting "people").
Last but not least, a reliable Backup policy with data off-load, either it being a Tape, a Virtual Tape Library or a Cloud Backup service (which differs from Cloud Storage).
06/09/2014 00:00:00